What is an Attack Surface?
The attack surface of your company is made up of all those areas that are potentially vulnerable to cyber attacks. These different areas, often called attack vectors, are where an unauthorized user can try to enter data or extract data from your environments. Think of your attack surface as a collection of points, system elements or endpoints that allow a hacker to potentially breach, effect or control your systems and extract or manipulate information for malicious purposes.
The attack surface is what is being attacked; the attack vector is the way in which a malicious actor gains access or control.
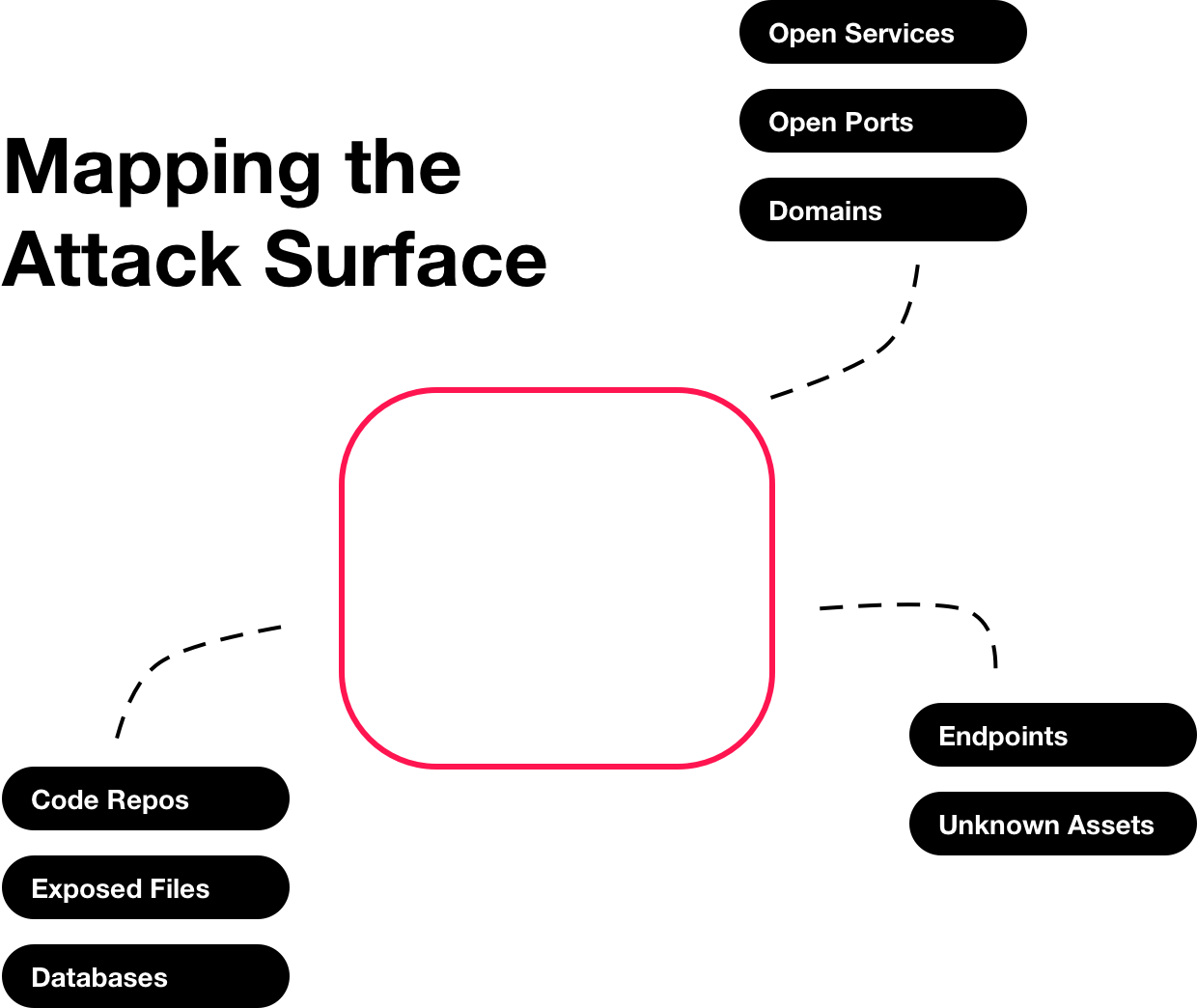
Elements of an attack surface
An attack surface composition can range widely between various companies, but often have the same elements:
- Domains and Subdomains (incl. third parties)
- IP Addresses and IP Blocks
- Internet Ports and Services
- SSL Certificates
- Public and Private Cloud
- Web Applications & Frameworks (Wordpress, Ruby/Python/Java/PHP, Apache, Nginx, etc.)
- Web Services (email, databases, APIs)
- Autonomous System Numbers (ASNs)
The less you know about your own attack surface and the larger it is, the harder it will be to protect from hackers. Mapping out your attack surface is a great first step to protecting your company from cyber attacks. Once you have an inventory of all the elements that make up your attack surface you will understand possible attack vectors and manage them.
Attack surface reduction
Let's look at how to reduce the attack surface of a company by following these steps:
- Map out your attack surface. Having an inventory of your attack surface allows you to see potential attack vectors. You should automatically monitor your companies attack surface for changes. You can do this for free with Templarbit.
- Reduce your attack surface. Ensure you remove internet connected assets that are not in use and reduce entry points available to untrusted users. Also consider limitting access of certain systems to fewer of your trusted users.
- Increase security measures. Your attack surface map will help you identify where to increase your security measures. Start by moving from the most critical assets or elements and the most vulnerable points to the least. Keep the system up to date, think through access controls and deploy security scans.
The initial analysis of your attack surface will act as your todo list. You won't fix every problem you find instantly but it gives you an accurate todo list to guide your work as you attempt to make your company safer and more secure.